In our increasingly mobile-first world, QR codes—once seen as handy shortcuts—have become ripe for exploitation. Cybercriminals have weaponized this convenience, giving rise to “quishing”: phishing attacks delivered via embedded QR codes that bypass traditional email filters and human detection.
Why Quishing Is on the Rise
- Convenient disguise, dangerous destination
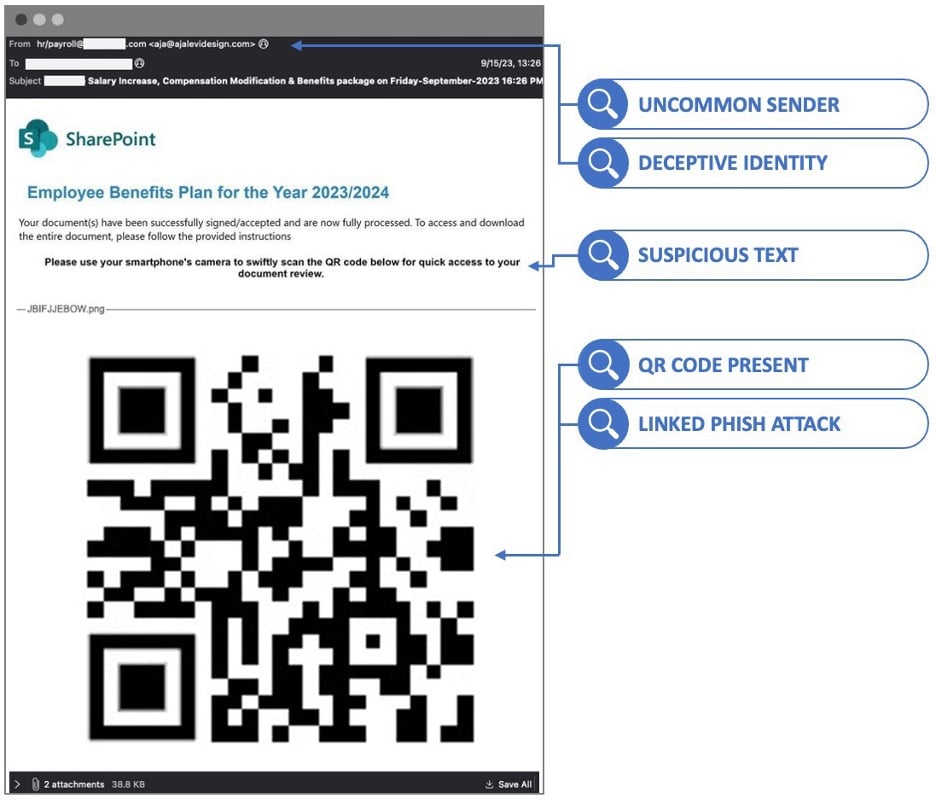
QR codes hide malicious URLs embedded within images or attachments—tricks that often fly under the radar of email security systems and recipients alike. - Explosive growth in usage
With QR code redemptions expected to hit 5.3 billion in 2025, attackers see significant opportunity to exploit the trend. - Statistical spike in attacks
- From June to August 2023, 8,878 quishing incidents were detected; QR-based phishing jumped from just 0.8% of phishing payloads in 2021 to 12.4% in 2023, maintaining a high level through 2024.
- A recent report identified over 4.2 million QR code phishing threats in early 2025 alone.
- Widespread impact across sectors
Quishing is affecting both individuals and organizations—millions of users have been targeted via malicious QR codes displayed in public spaces like parking meters and posters.
Real‑world Quishing Scenarios
- Parking meter scams
Fraudsters stick counterfeit QR codes over legitimate ones, redirecting unsuspecting users to fraudulent payment pages. One reported victim lost £13,000 in a single incident. - Email-based traps
QR codes embedded in emails—sometimes disguised with logos or urgent messaging—redirect recipients to fake login pages, especially targeting Microsoft credentials. - Advanced phishing experiments
Academic studies confirm quishing can be as effective as traditional phishing. In one controlled test, users clicked through QR code-based phishing at equal rates to traditional phishing emails, yet the approach is harder for systems to flag.
Mitigation Strategies for Your Organization
- Train employees to treat QR codes like suspicious links
Never scan QR codes from unexpected or unsolicited sources. Encourage staff to report suspicious emails—either via Outlook’s “Report Message” button or similar tools. - Promote URL review before inputting credentials
After scanning, always check that the website domain and URL look legitimate and are secured (e.g., correct spelling, HTTPS). - Deploy technical safeguards
If you’re not already, consider subscribing to our 24×7 MXDR and ITDR services, which enhance detection and response capabilities tailored to sophisticated threats like quishing. - Stay one step ahead with awareness
Use visuals like the one above in internal campaigns to remind staff that QR codes can be phishing vectors.